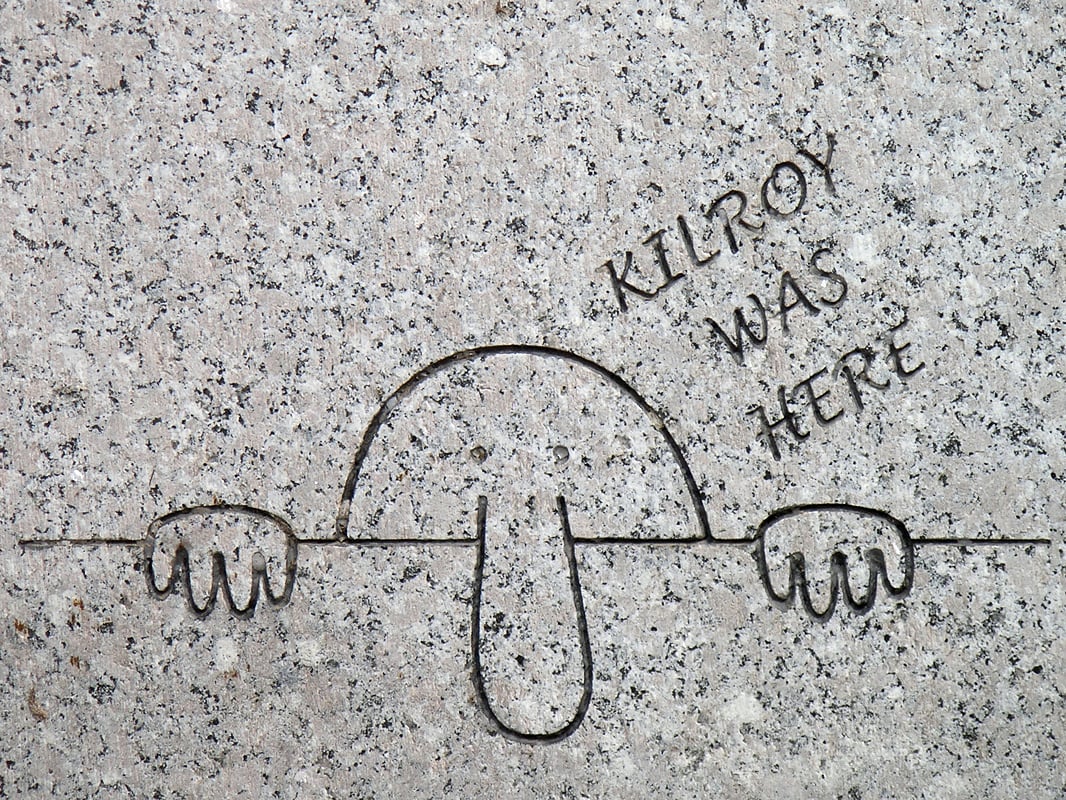
Google is expanding its regular “transparency report” to include some broad statistics on the numbers of national security letters it receives from the US government. It’s a significant step for the company to publicly disclose what it privately tells the authorities about its users, and it gives us some more insight into how the government monitors the vastness of the Internet.
The numbers Google is reporting are broad. But the big takeaway here is that the FBI–the primary user of national security letters–appears to be interested not so much in the content of a person’s email, but rather in what’s known as “basic subscriber information,” more high-level data such as a person’s name, address, and the length of service on his account. This information is potentially more useful, and surely easier to get, than the written contents of an e-mail.
At first glance, the numbers of NSL requests Google is reporting look “awfully high” for one company, says Cato’s Julian Sanchez, who breaks down the report and places it the context of what we already know about how NSLs, which are notoriously opaque tools for secretly obtaining information, are used.
Comparing the Google numbers for NSLs to those released by the Justice Department, one might conclude that the company received one-seventh of all NSL requests, something Sanchez concludes “seems impossible.” Google is big, but not so big that it would account for an outsized share of all NSLs relative to every other company that receives them. Telecommunications companies, including phone and Internet service providers, as well as financial institutions regularly get NSLs, which require companies to hand over different kinds of information short of the actual content of a message.
So why are Google’s numbers so high? Sanchez persuasively argues that Google is counting requests for basic subscriber information, and that the Justice Department, in its own NSL reports, is not. Looking at Google’s numbers, it would appear that the “overwhelming majority” of NSL requests it receives are for this basic subscriber information, Sanchez writes, which suggests, troublingly, “that the total number of Americans affected by all NSLs is thus vastly, vastly larger than the official numbers would suggest.”
I think Sanchez is right. And it makes sense based on what we know about how law enforcement and intelligence agencies use electronic information to track people and monitor the Internet for various threats.
For instance, shortly before the 9/11 attacks, the National Security Agency asked Qwest Communications for subscriber information on its then-quickly expanding communications network. The NSA’s goal was to monitor the Internet for potential cyber threats against the government. (This was years before cyber security became de rigueur in national security circles, so this was a very foresighted move by the NSA.) After the attacks, the NSA again made the request, this time for tracking terrorists.
Qwest refused, however, after concluding that access to such detailed customer information was illegal without a warrant. Qwest executives and lawyers decided that even though the information wasn’t technically “content,” it was still revealing enough that giving it to the government required some legal approval.
This is an important point. Call logs and records of phone calls may be called “basic” information under the law, but they are full of rich, potentially illuminating information about a person. Today, government agencies, including the NSA, use basic data, particularly phone logs and Internet addresses, to create detailed pictures of a person’s communications and his associations. It doesn’t really matter, in this context, that the data doesn’t include the text of an e-mail or the spoken words of a phone call.
The Google disclosure underscores the extent to which the government is after this kind of general data, more so than actual content. National security letters are not warrants, but they’re being used today to obtain information of the kind that the NSA wanted from Qwest. This should come as no surprise, given how well the NSA, and the FBI, anticipated the ways that digital technology would transform communication, and how that would, in turn, give the government new opportunities for collecting information.
The way the FBI is using national security letters today, if Sanchez’s analysis is correct, suggests that written e-mails aren’t really what investigators want most. It’s easier under the law to get basic information, and that information can tell them a lot about their targets, often more than the text of an e-mail itself. Think about it: How likely is a suspected terrorist to spell out his intentions in a message? You’d learn a lot more about his capability to do harm by positioning him within a bigger terrorist network, and you can understand and illuminate that network with the kinds of information that Google and other NSL recipients provide. This broad information is also useful to investigators when they’re trying to identify individuals who they can scrutinize more closely with searches that require a warrant.
The other reason why a government agency would want this kind of basic information? “To effectively de-anonymize the otherwise unknown user of a particular account,” Sanchez says. That’s just what investigators did when they determined that Paula Broadwell was sending anonymous e-mails to a friend of Gen. David Petraeus. Sanchez speculates that this digital de-cloaking may be “the primary reason” an agency would ask Google for basic subscriber information.
There’s an important wrinkle in all of this. Google also said that when it receives NSLs, it doesn’t disclose Internet protocol addresses. “Since these can be crucial to linking a wide array of online activity to a particular user, their exclusion would somewhat limit the potential of NSLs to undermine Internet anonymity,” Sanchez writes. But it could be that this exclusion is just a Google policy. Sanchez concludes that “it is not at all clear whether other providers will disclose IP addresses in response to NSLs.”
We should also keep in mind that NSLs are not the only means by which companies share information with the government, nor are IP addresses the only way to unmask someone or provide useful intelligence for investigators. Nevertheless, this is an enlightening report, and it adds to the ever-accreting body of details about how the government watches us, and what companies are doing to comply with the law and at the same time protect their customers’ information. Never an easy balance. It’ll only get harder.