Nine FBI agents sued the US Department of Justice Tuesday, saying that the Trump administration’s efforts to identify bureau officials who worked on cases related to January 6 and President Trump’s documents case could place “themselves and their families in immediate danger of retribution by the now pardoned and at-large Jan. 6 convicted felons.” Trump pardoned most of the January 6 defendants on the first day of his second term.
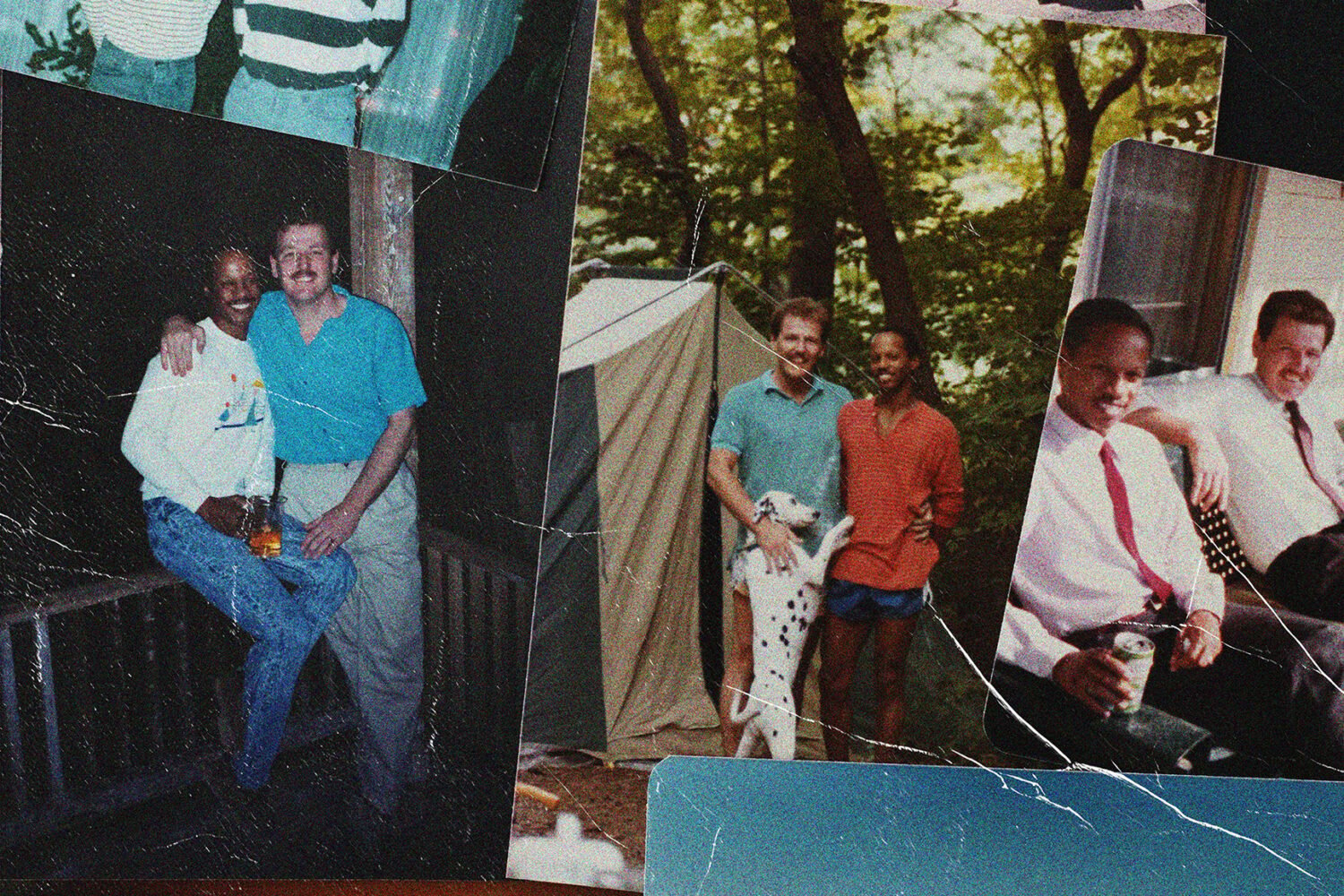
The lawsuit, filed in federal court in DC Tuesday, includes images of the questionnaire the department sent out last weekend as part of an effort to investigate the investigation into the riot at the Capitol, the largest investigation in US history. The plaintiffs, who filed anonymously, say they believe that the “purpose for this list is to identify agents to be terminated or to suffer other adverse employment action.” The contents of the list are likely to be published by the administration, the plaintiffs say, which would violate their First and Fifth amendment rights, as well as violate federal law.
More than 6,000 people could constitute a class for the suit, the plaintiffs argue. They ask the court to block the “aggregation, storage, reporting, publication or dissemination of any list or compilation of information that would identify FBI agents and other personnel.”
The Department of Justice has not yet replied to a request for comment about the suit.
FBI agents’ lawsuit by Washingtonian Magazine on Scribd
DOJ questionnaire for FBI employees by Washingtonian Magazine on Scribd