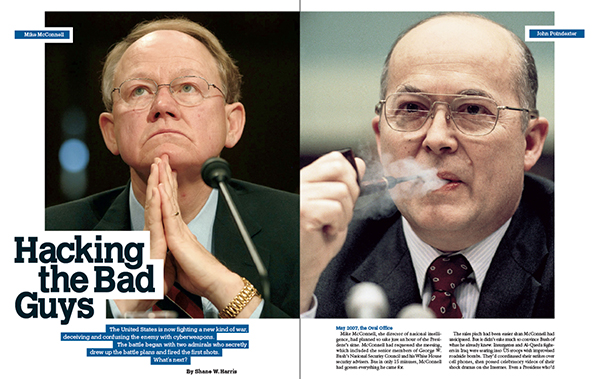
Mike McConnell, the director of national intelligence, had planned to take just an hour of the President’s time. McConnell had requested the meeting, which included the senior members of George W. Bush’s National Security Council and his White House security advisers. But in only 15 minutes, McConnell had gotten everything he came for.
The sales pitch had been easier than McConnell had anticipated. But it didn’t take much to convince Bush of what he already knew. Insurgents and Al-Qaeda fighters in Iraq were tearing into US troops with improvised roadside bombs. They’d coordinated their strikes over cell phones, then posted celebratory videos of their shock dramas on the Internet. Even a President who’d only used “the Google” to find an overhead photo of his Texas ranch understood that the Iraqi insurgency had a technical dimension.
To counter these enemies, Bush had ordered a 20,000-strong “surge” of troops. But McConnell proposed another angle, a way to attack the increasingly vicious network of roadside bombers without firing a bullet. He wanted to use the intelligence community’s expertise to take control of a communications network. He wanted to hack the insurgency.
The National Security Agency had, under McConnell’s tenure as director in the 1990s, established an “information warfare” unit that could break into adversary computer networks with weapons fashioned not of steel but of computer code. NSA—the largest American intelligence agency—was a massive digital eavesdropper, adept at plucking phone calls and other electronic communications off the global telecom network or out of the air as the signals bounced off satellites. The information-warfare unit would expand on those skills by cracking into computer systems—not just to spy but to play with an enemy’s mind, to corrupt and undermine its confidence in its own intelligence. Scrambling communications. Falsifying messages and coordinates.
Denial and deception were ancient techniques of war, and McConnell had helped package them into modern weapons. Now he wanted to unleash them in Iraq—in a cyberwar.
Bush quickly approved the operation, which required presidential authorization because cyberweapons had a way of getting out of hand. In the months before the 2003 invasion of Iraq, military planners had nixed a plan to knock out Saddam Hussein’s banking system with a computer virus because they feared it could infect the global banking system.
When the military and the intelligence community put the new plan into action, it was more focused. US forces sent messages that looked as if they’d come from one of the insurgents’ own but that actually led them into the fire of American soldiers. Being inside the enemy network afforded valuable tactical and strategic advantages, not the least of which was access to a virtual map of everyone in a bombing cell. The full force of American digital surveillance was brought to bear.
Other streams of intelligence—particularly from unmanned aerial drones and Iraqi informants—gave US troops and special-operations forces the richest trove of information they’d had in the history of the war. It was this electronic data, more than any troop surge, that Bush-administration officials later credited with turning the tide of the war.
McConnell had been prepared to take the full hour to explain cyberwarfare to the President. But now there he was in the Oval Office, surrounded by senior members of the Cabinet and the President’s national-security team, with 45 minutes left on the clock. Well, he thought, as long as we’re here.
There was something else McConnell wanted to tell the President: America’s vital systems of communication and industry—the same kinds of networks that America would eventually attack in Iraq—were wide open to an attack from America’s enemies.
Here, too, the former NSA director was a seasoned expert. Before returning to government, McConnell had run the intelligence division of Booz Allen Hamilton, a leading Beltway contractor stocked with former high-ranking officials. Cyberdefense was his pet project. McConnell found that the digital telecommunications networks proliferating across the globe were good targets for hackers, foreign governments, and potentially terrorists.
His Booz Allen team zeroed in on weaknesses in financial-services companies. Working with officials from the New York Stock Exchange, he developed a report about how hackers could break into major banks’ electronic accounting systems and steal or alter data. Such an assault could erode the system of trust and assurance upon which the US economy rested—banks unable to close transactions, clearinghouses unable to process trades.
McConnell had a rare grasp of the cyberthreat, against which the United States still hadn’t amassed its forces. He had risen to national prominence in the early 1990s as director of intelligence for the chairman of the Joint Chiefs of Staff, Colin Powell, during the Gulf War. McConnell, then a vice admiral, so firmly grasped the minutiae of troop movements and the concepts of broad military strategy that Powell put him in charge of daily press briefings. McConnell had to explain the war effort to the American public in a digestible format. Now, as the President’s top intelligence adviser, he could speak directly to the commander-in-chief.
McConnell decided to tell President Bush just how defenseless American banks, power grids, and other critical sectors that ran on the Internet really were. Everything that McConnell had just described about cyberwarfare—about what the United States could do in Iraq—others could do to the United States.
Bush looked incredulous. This could happen here? Phone systems were vulnerable? The President pointed to the secure phone on his desk and asked whether someone could electronically hack his way into it.
“If the capability to exploit a communications device exists,” McConnell said, “we have to assume that our enemies either have it or are trying to develop it.”
He described the problem in words that would resonate with Bush: “If the 9/11 perpetrators had focused on a single US bank through cyberattack, and it had been successful, it would have had an order-of-magnitude greater impact on the US economy than the physical attack.”
Bush turned to Henry Paulson, his Treasury Secretary and the former CEO of Goldman Sachs: “Is this true, Hank?”
Paulson said it was. He told Bush that his worst fear at Goldman had been that a hacker might play with the data of a major financial institution. Corrupt it. Undermine it.
Bush stood up. “This is our competitive advantage for the next 70 to 100 years,” he said. “Certainly we have to do what’s necessary to protect it.”
“McConnell,” Bush said, turning to his spy chief, “you brought this in here. You’ve got 30 days to develop a plan.”
McConnell’s plan quickly morphed into a classified program to shrink the thousands of points at which government computer systems were physically connected to the public Internet to fewer than a hundred. The administration would fend off any electronic onslaught by bringing up the drawbridge. McConnell also wanted NSA to stand point on defense of military and intelligence networks by monitoring their connections for signs of hackers.
It took months of interagency negotiations and bureaucratic turf wars, but in the end the ambitious plan earned an apt name: the Comprehensive National Cyber Security Initiative. Never before had the government’s intelligence and security agencies taken such an active role in policing the Internet. The plan remained classified because, in addition to the defensive strategy, Bush authorized an offensive component—the ability to attack threats to America in cyberspace.
McConnell could congratulate himself for getting through to Bush. But it wasn’t the first time a veteran security official had warned the commander-in-chief about the threat to American security lurking in the digital cloud. The path to McConnell’s fateful meeting in the Oval Office had been blazed almost a quarter century earlier, when a fellow admiral convinced his commander-in-chief to pay attention to a new problem.
September 1984: The Roosevelt Room
Ronald Reagan made only one public appearance on Monday, September 17. Before cameras and journalists, the President received the report of the US-Japan Advisory Commission, a wide-ranging policy review headed by Hewlett-Packard chairman David Packard. The only remarks Reagan made were to turn the meeting over to Packard, who spoke about the importance of Japanese-American cooperation and then read a long note from his Japanese co-chairman. “Well, God bless you all. Thank you very much,” Reagan said, and wrapped up the meeting for the cameras.
The President’s rather banal public schedule stood in contrast to the momentous decisions playing out behind the scenes that morning. His deputy national-security adviser, Vice Admiral John Poindexter, had crafted a highly technical and ambitious national-security order for the President’s signature. It was a plan for government to defend a vulnerable national asset—cyberspace.
It was fitting that the head of a major US technology company was in the White House that morning. Poindexter had pointed out that the only way to secure the nation’s expanding and little-understood computer networks was to forge a new alliance with the private sector. American corporations, after all, were the source of the nation’s technical innovation and owned these networks. One of Poindexter’s biggest concerns was protecting the government information that moved over them, particularly the details about a nascent counterterrorism operation he had been overseeing since the previous year.
On the morning of October 23, 1983, a suicide truck bomber had plowed into the barracks of a Marine unit stationed in Beirut, who were there as part of an international peacekeeping force to deal with the ravages of civil war in Lebanon. The bomber killed 241 American servicemembers, most of whom were sleeping in their bunks. The Beirut attacks spurred Poindexter’s compulsive need to make order out of chaos, which was the operative word in Lebanon.
After the bombing, investigators revealed that since May, the intelligence community had fielded more than 100 warnings about car bombings in Beirut. But no one had given the alerts any particular weight, nor had they been shared with the military chain of command. An earlier attack on the US embassy in April had killed 63 people, including most of the CIA station in Beirut.
A forensic analysis by the FBI revealed evidence of an innovative terror group in the city trying to fashion devastating bombs out of everyday materials. But the FBI’s findings were never shared outside the bureaucratic silos of the CIA or the State Department. They were just one more signal thrown onto a pile that eventually included one dreadful message: an NSA intercept of terrorist communications that actually indicated the Marine-barracks attack but that military commanders didn’t receive from their subordinates until days after the bombing.
Poindexter was one of the Navy’s rising stars, at the top of his Annapolis class of 1958, and seemingly destined for the service’s top job, chief of naval operations. His ascent had been orderly, but when he arrived at the White House in 1981 as a military assistant, the lack of consistency and discipline there appalled him. He told more than one friend it was like setting out to sea with no orders. In the fallout of the Beirut surprise attack, he saw an opportunity.
Poindexter had come to the White House with a mandate to get things there under control. His primary task, per the President’s top security advisers, was to update the White House Situation Room with modern telecommunications. He’d set up a $14-million Crisis Management Center in the Old Executive Office Building, installing videoconferencing systems, wall-mounted video screens, and links to the classified systems that ran diplomatic, military, and intelligence cable traffic. Poindexter turned this technological outpost into a data center for coordinated counterterrorism. This would be the hub of a new enterprise aimed at breaking down barriers and sharing information across protected turf.
Reagan had promoted Poindexter to deputy national-security adviser only a week before the Beirut bombing. Now the admiral was in a position to make people move. The attacks sharpened everyone’s focus.
But there was a problem. With all of these new linkages among the intelligence community, the State Department, and the Pentagon, a foreign power, particularly the Soviet Union, had more chances to hack into the network. Poindexter wanted to stop any hemorrhage of data before it happened.
His cyberdefense plan, labeled National Security Decision Directive 145, laid bare the problem in its first paragraph: “The technology to exploit these electronic systems is widespread and is used extensively by foreign nations and can be employed, as well, by terrorist groups and criminal elements.” Both the government and American business were “targets of foreign exploitation.”
The year was fitting: 1984. America was gripped by stories&mdash
;some fanciful, some real—about the apocalyptic dangers looming in the vast network of wires and cables that carried an increasing flow of bits and bytes. Only a year earlier, the movie War Games had told the story of a precocious high-school student who used the computer in his bedroom to find a back door into the military’s central computer system, nearly triggering an automatic launch of the US nuclear arsenal.
The movie might have taken some liberties, but it had a mirror in reality. The same year, the FBI was on the trail of a band of computer hackers who had penetrated systems at Los Alamos National Laboratory, a large bank headquartered in Los Angeles, and Memorial Sloan-Kettering Cancer Center in New York City. Calling themselves the 414s, the hackers were eventually found to be a group of six teenagers who drew their name from the area code of their hometown, Milwaukee. The boys had met in a local Explorer Scout troop.
Poindexter was more worried about foreign spies and terrorists than about high-schoolers. But in cyberspace, the threat was all the same.
The presidential directive, which Reagan signed without fanfare, set up several layers of committees and staff to deal with the government’s end of the problem—the gaps in its own systems. But buried within the technocratic language was a single line that proposed a radical shift. A national committee, chaired by a senior Pentagon official and composed of representatives from the FBI, the CIA, the State Department, NSA, the military services, and the NSC staff, among others, would identify systems that handled “sensitive, non-government information,” which, if lost or exploited, “could adversely affect the national security interests.” Where appropriate, the committee would assist the private sector “in applying security measures.”
Poindexter wanted the government to take control of protecting the nation’s network. And, as skeptical outsiders in the electronic-privacy community soon pointed out, Poindexter himself wanted to be in charge.
To control the new cyberbureaucracy, the directive installed a “steering group” chaired by the President’s national-security adviser. Poindexter was just the deputy then, but he’d long since divided the duties of running the NSC staff with his boss and fellow Academy man, Robert “Bud” McFarlane, who handled the political tasks of the job, particularly meeting with Congress and the media. Poindexter actually managed the guts of the National Security Council. He was the behind-the-scenes power.
Not a single piece of paper that touched national-security policy moved through the West Wing without Poindexter’s eyes falling on it. In 1986, Reagan elevated him to the top slot, national-security adviser to the President. But even before that, soon after Reagan signed the cyberdirective, it didn’t take long for Poindexter’s enemies in the privacy community to single him out and dub him a would-be “computer czar.”
Poindexter’s plan for cybersecurity was extraordinary on two levels: It inserted government supervision into private affairs, and it asserted a national-security interest in unclassified information.
Poindexter realized that secret information wasn’t the only target on the network, and perhaps it wasn’t even the most important. But his strategy for addressing the threat struck some as one step too far. Even the General Accounting Office, Congress’s investigative arm, found that the order vaguely defined the term “sensitive but unclassified information” in such a way that innocuous facts used to make policy decisions could be swept behind a curtain of secrecy. One expert witness told Congress that under the broad presidential directive, the government might try to classify important public information such as flight-safety reports or monetary-policy data held by the Federal Reserve.
Poindexter had tripped the thin line separating public and private interests. It was the first indication that to strike a balance between security and liberty, the government and its citizenry would take opposite sides. Poindexter invited the struggle.
He took up that fight again almost 20 years later. After the 9/11 terrorist attacks in 2001, Poindexter led a Defense Department research program that he dubbed Total Information Awareness. It aimed to take his 1980s concept for harnessing the collective intelligence power of government to a new level. TIA wouldn’t just sift through government databases for signals of imminent crises; it would gain access to private data as well. Poindexter imagined searching through flight reservations, credit-card receipts, and even veterinary records for patterns of transactions that indicated some stage of a terrorist plot.
Once again he traded blows with the civil libertarians who had ridiculed his cyberplan in 1984. The country became embroiled in an argument that would outlast Poindexter’s tenure in the Reagan administration: Should the government be allowed to monitor its own people—and control their information—in order to protect them?
Poindexter posed the question, and McConnell took it up a quarter century later. But another leader would give the answer.
May 2009: The White House East Room
Barack Obama had been hacked once. Over a two-month period at the end of his presidential run, intruders accessed his e-mails and campaign files, including policy position papers and the candidate’s travel plans. Law-enforcement officials later theorized that the hackers either were based in China or were working for its government. The teenage hackers of War Games had been replaced by old-fashioned spies hip to a new game. They’d concluded that it was easier to crack a nation’s secrets with a keyboard and a mouse than with a mole and a bag of cash. The same hackers who gamed Obama were believed to have busted his rival, John McCain. The cyberspies wanted to cover their bases by hitting both campaigns.
The incident hadn’t embarrassed Obama. It emboldened him. He stood before lawmakers, Cabinet officials, and journalists in the East Room and came clean: “I know how it feels to have privacy violated, because it has happened to me and the people around me.” Obama admitted that his computers had been hacked, and he said that it fit a pattern of stealthy activity that imperiled American security.
The President had called the conference to announce his new national cybersecurity strategy. Obama hardly needed to be convinced of the transformative power of the Internet. His campaign had organized much of its support, including its vaunted fundraising apparatus, in cyberspace. But now he’d become acquainted with the dark side of the Net, both from the campaign hacking and from some advice he’d received from a sage of the cyberwars.
After Obama had secured the Democratic presidential nomination, Mike McConnell, still director of national intelligence, gave the candidate his first secret-level national-security briefing. Toward the end of the meeting, which focused mostly on terrorist threats, Obama asked McConnell what else should be on his radar if he won the election. Cybersecurity, McConnell told him. For all the work the Bush administration had done to shore up the national defenses, it was merely a first step.
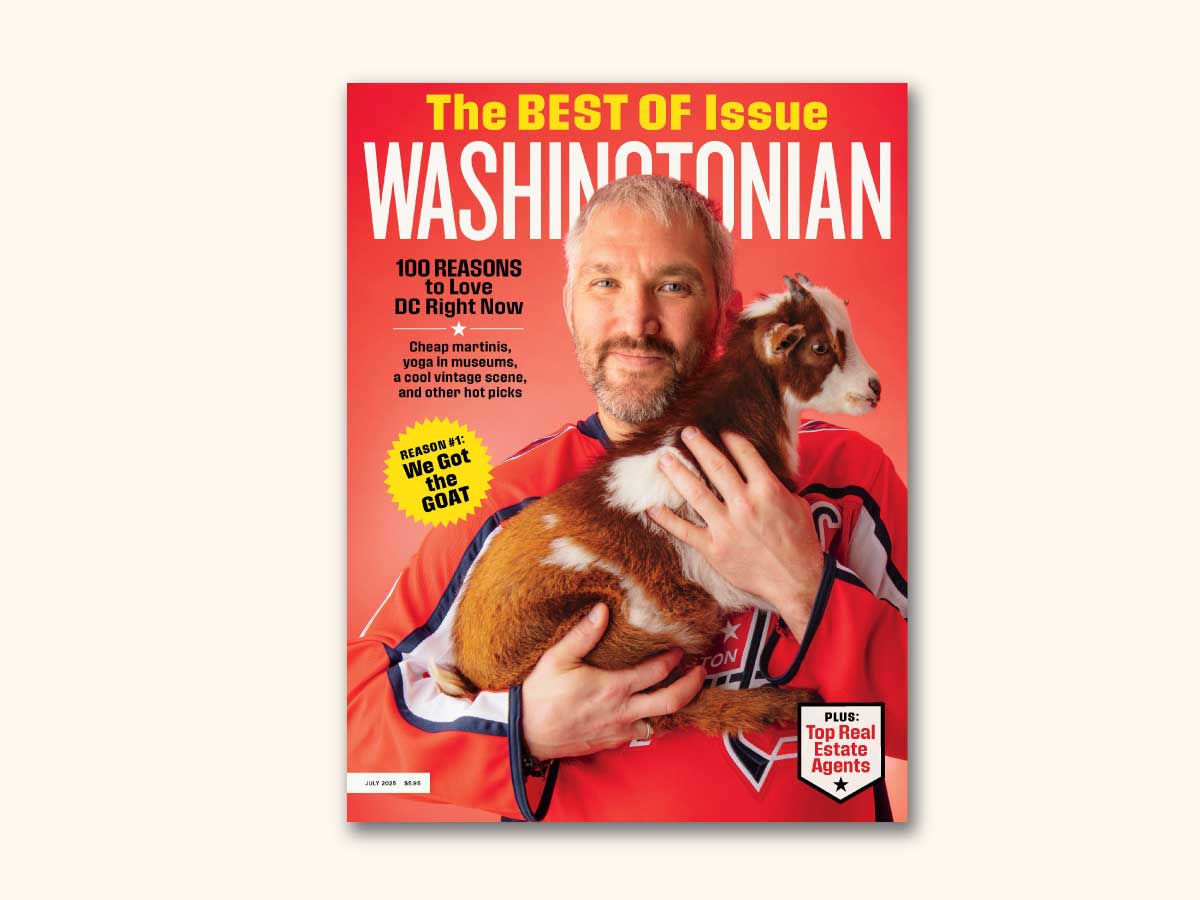
Obama aimed to get ahead of the threat. The crowd in the East Room hoped to hear the President pick a new cybersecurity coordinator, based at the White House, which the techno-cognoscenti had already dubbed the “cyberczar.” The United States needed a new commander in the digital war.
Obama met their demands, but only halfway. During his campaign, he had pledged to appoint a cyberchief who’d report directly to him. But now the President said the so-called czar would have “regular access.” It was a demotion. The job would also sit lower on the totem pole of the National Security Council staff and report to two masters—the national-security adviser, Jim Jones, and the director of the President’s National Economic Council, Larry Summers.
In the months before the unveiling of the cyberstrategy, Summers had prevailed upon the President to bifurcate the position. Those close to the White House’s evolving take on the role of the cyberczar saw Summers trying to exert control over any new regulations that the security official might dream up. Clinton-era offic
ials had taken the same tack in the 1990s. Although experts forcefully warned the administration about the blooming security risks posed by an interconnected world—and Mike McConnell, as director of NSA, was among their ranks—President Clinton was reluctant to take any action that could stymie business and technological innovation on the fast-expanding Internet. Security has always been the bane of creativity.
But Obama was moving publicly, in a way no President ever had, because the stakes had never been higher. “Every day we see waves of cyberthieves trolling for sensitive information,” Obama said. “The disgruntled employee on the inside, the lone hacker a thousand miles away, organized crime, the industrial spy, and, increasingly, foreign intelligence services.” Obama cast the net wide, framed the threat for what it was—all-encompassing.
These were chilling stories regardless of who recounted them. But the President went a step further and admitted that the most dire warnings of the nation’s cyberdefenders were already coming to pass. “We know that cyberintruders have probed our electrical grid and that in other countries cyberattacks have plunged entire cities into darkness,” Obama said. A moment later, he acknowledged that cyberspies had also broken into secret US military networks.
“This cyberthreat is one of the most serious economic and national-security challenges we face as a nation,” Obama declared. “From now on, our digital infrastructure—the networks and computers we depend on every day—will be treated as they should be: as a strategic national asset.”
In December, Obama tapped Howard Schmidt, a former chief security officer at Microsoft, as his cyberczar; Schmidt had also been an adviser to George W. Bush. Meanwhile, the government moved with new vigor to secure its own sensitive networks. The comprehensive plan that McConnell had helped launch in 2007 saw his old agency, NSA, take point in protecting military and intelligence agency networks. The Department of Homeland Security, which holds the legal responsibility for protecting civilian computer systems, would receive “technical assistance” from NSA—a polite way of saying that most of the expertise to actually perform the department’s mission would come from the country’s largest intelligence agency.
Today there’s little doubt that the federal bureaucracy has found a new center of gravity for the cyberthreat. The President’s strategy is predicated on one fact: The military and the intelligence community employ the most and best cyberexperts required to fight a war on the Internet. And the government does view the problem as a war. Obama said as much when he called cyberthreats “a matter of public safety and national security. We count on computer networks to deliver our oil and gas, our power and our water. We rely on them for public transportation and air-traffic control. . . . Our technological advantage is a key to America’s military dominance. ”
Obama grasped the facts that had menaced his predecessors, but he has gone further than any of them by describing the threat so vividly and by not hiding its true nature and scope. The President of the United States had stood before the nation and said, yes, I’ve been hacked. We’ve been hacked. This problem is real. And it is dangerous. And you can blame me if we don’t fix it.
It’s a reality of Washington that a powerful idea can take a generation to materialize. John Poindexter might not have hoped that his plans for defending the Internet would sit untapped for so long, but he wouldn’t be surprised. He has long adhered to a view of how real change happens in Washington. People, not policies or technology, are the most intransigent forces. Until they come around, there’s no meaningful progress.
Poindexter, now 73, remains a quiet and vital force in national-security circles. He keeps a small home office in the modest two-story colonial in Rockville that he’s occupied since his days at the White House. The room is adorned with memorabilia of an official life in the Navy, and one wall of an adjoining family room is covered by photographs of him and Reagan in the Oval Office.
Poindexter has never truly left the scene. Some of Obama’s and Bush’s senior security advisers are longtime friends of the admiral. He moves in a rarefied environment occupied by the graybeards of American spycraft. He also sits on the board of directors of Saffron Technology, a start-up that builds high-end information-processing software for the military and intelligence community. In his off-hours, Poindexter tends to his sailboat, Bluebird, which he moors near Annapolis.
Meanwhile, McConnell, 66, has made securing cyberspace his professional and personal mission. After leaving the Bush administration last year, he returned to Booz Allen Hamilton, to the same corner office he occupied before coming back to government. From his private conference room, adorned with photos of him and President Bush, there’s a panoramic view of planes taking off and landing at Dulles Airport.
Cybersecurity has become de rigueur among national-security mavens in Washington, and it’s hard to attend any of the cyberevents hosted around town without seeing McConnell’s face or hearing his name invoked. Recently, the International Spy Museum installed a new cyberexhibit called “Weapons of Mass Disruption.” There’s McConnell, on a wall-mounted screen, explaining the threat to power grids and banks, just as he did for George W. Bush.
Poindexter and McConnell are human bookends in the Washington saga—one the idea man, the other the closer. What remains of the story now is largely beyond their control. Each man is an influencer, and McConnell has a personal stake in the outcome—his unit at Booz Allen is pursuing cybersecurity business. But both admirals have set sail into their twilights.
They seem to have a certain peace with that. As animated as they become about what’s left to be done, about the threats that remain, they’re shrouded in a kind of wisdom that accrues with age. It’s the air not of a man who knows he’s right but of one who knows he did all he could. Barack Obama inherits their story. And McConnell and Poindexter watch as the next chapter is written.